You can roll out an app only to a subset of your users in Kubernetes using canary releases with Istio, Kiali and the Gateway API.
Let's start by looking at an example.
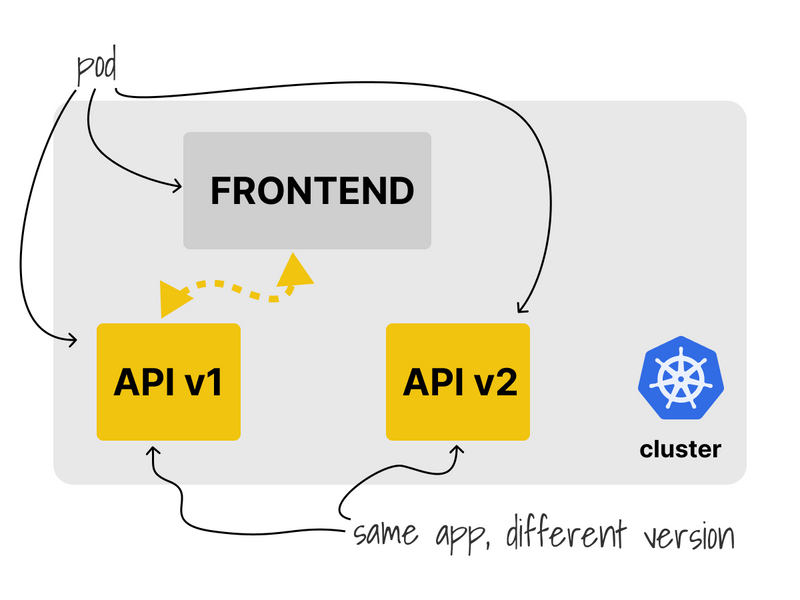
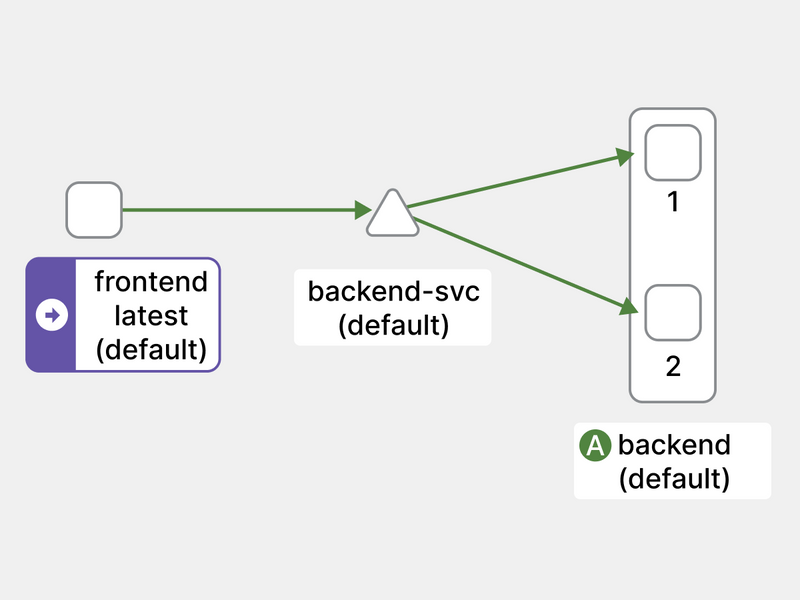
The current cluster has three apps:
- A backend that exposes an API at version v1.
- Another app on version v2.
- A frontend component that consumes the API.
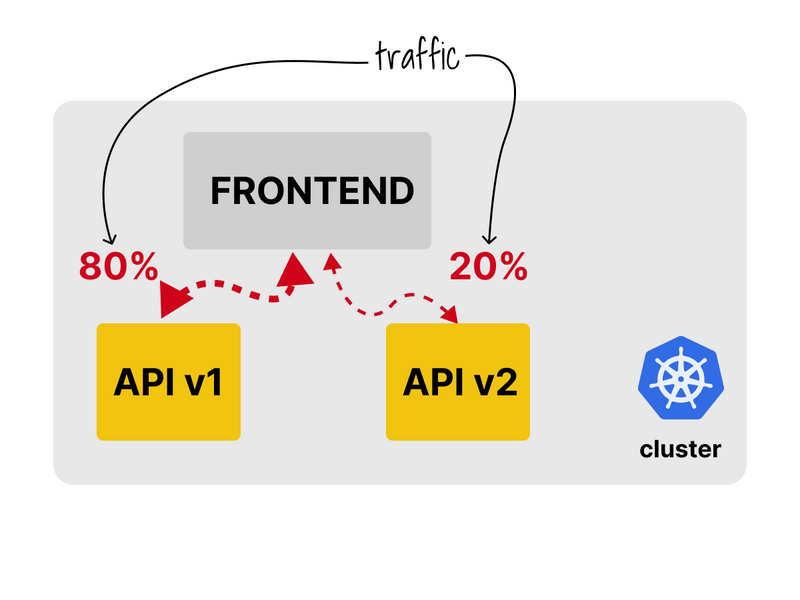
Ideally, the frontend should consume 80% of requests from v1 and only 20% from v2.
But how?
You can use a Service Mesh for that.
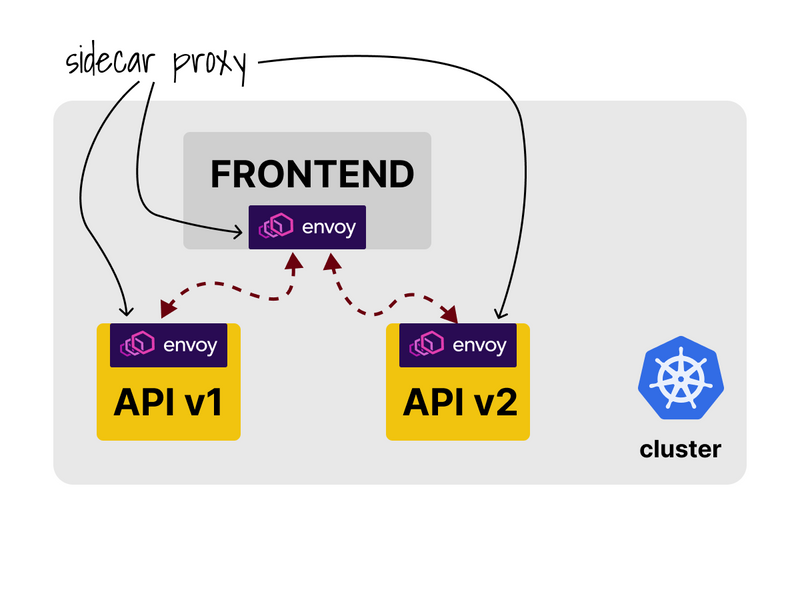
As soon as you install the service mesh, each pod in the cluster gains an extra container.
The container proxies all the outgoing and incoming requests.
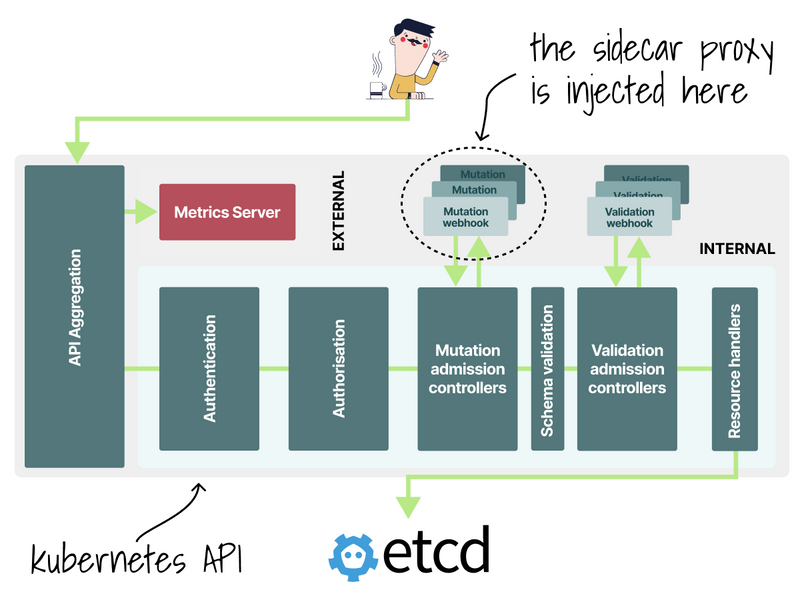
The proxy is automatically injected using a mutating webhook.
Before the pod is stored in etcd, the YAML definition is modified, and the proxy is injected.
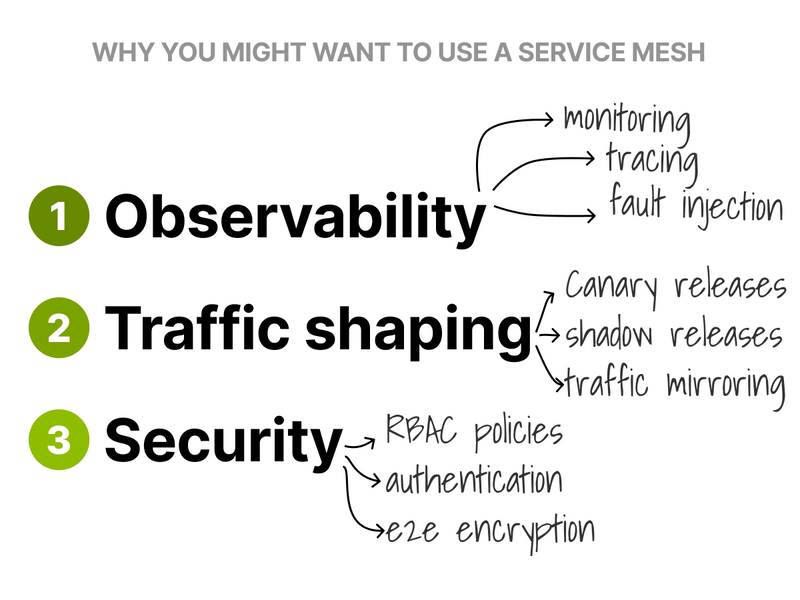
A service mesh is helpful because you can:
- Monitor metrics.
- Trace dependencies between components.
- Decide traffic splits.
I generated some traffic to test it and used Kiali to trace it.
It automatically mapped all the components and the direction of the traffic.
All without any hints from my side!
What about the canary release though?
You can use a service mesh to fine-tune how much traffic each app consumes.
To test it, I created an 80-20 split between the two backends.
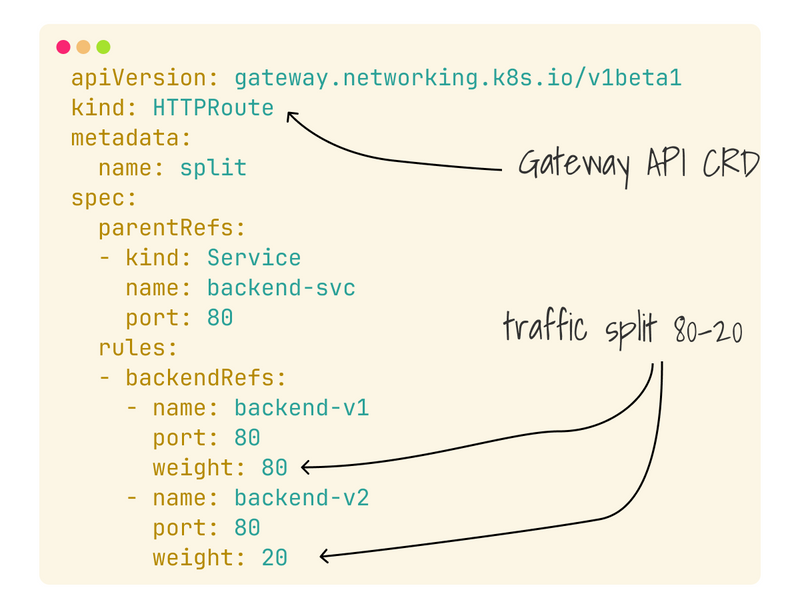
In this example, I'm using an HTTPRoute:
HTTPRoute is an object part of the Gateway API that lets you gradually increase and decrease the traffic and which you can use to transition from an 80-20 split to 0-100.
Service meshes can also:
- Help you roll out shadow releases.
- Encrypt intrapod traffic.
- Mirror traffic between cluster.
- Inspect and rewrite traffic.
- Enforce policies.
- Inject faults to test the resilience.
And more!
Which one should you use?
At Learnk8s we've put together a spreadsheet to compare them.
And finally, if you've enjoyed this thread, you might also like:



Top comments (15)
I request that you keep me informed about news updates. Additionally, please add contemporary articles for our continual reading. Baseball Bros IO is an exciting online baseball game .
Very informative article on traffic shaping with Istio and Kubernetes. It's fascinating to see how these tools can be used for canary releases. For more insights on Istio, check out this great resource: scritchy scratchy.
Great article! The step-by-step breakdown of using Istio and Kiali for canary deployments in Kubernetes is super helpful. The visuals really clarify how traffic splitting works.
Geometry Dash
The program is made to use the API on the back end. It works with version v2 papa's pizzeria, which might have new features, better performance, or different functions than the previous version.
Matheus Valadares created something timeless with Agario It's one of the rare games where players from all over the world can jump in instantly and understand how to play within seconds.
I find this forum very helpful, especially for those working in product development. There may be no complaints about nitrile gloves at the moment curve rush game, but that doesn't mean they can't be improved further using the suggestions shared here.
Perfect — this is a great setup to demonstrate a canary release using Istio, Kiali, and the Gateway API in Kubernetes. Let’s walk through melon playground how you can gradually roll out version v2 of your backend API to a subset of users while keeping v1 live.
I tried using HTTPRoute in Gateway API to adjust traffic and I have to say it is very flexible, making the transition from 80-20 to 0-100 extremely smooth. It felt like I was playing Sprunki Retake , controlling each step precisely to get the optimal result! Service meshes are equally powerful, supporting everything from shadow releases to securing traffic between pods, really expanding my knowledge of Kubernetes.
Customization is another fun element of Geometry Dash Lite. As players complete levels and achieve milestones, they unlock different cube icons and color options. These rewards let players personalize their in-game character, adding a layer of progression and self-expression to the gameplay.
The graphics in Snow Rider are colorful and charming, adding to the festive atmosphere.