It’s important to be able to audit user activity in Azure, whether you are dealing with a security incident or just want to fully review the actions a user has taken.
If one of your developers has their account compromised, reviewing their user activity can be a necessary task to ensure that they haven’t done anything malicious to your Azure account and resources, or exfiltrated data like access keys or secrets.
In this guide, we’ll show you how to retrieve all the activity logs for a given user in Azure to quickly assess the scope of the threat.
How to Get User Activity From Azure Logs
Azure Monitor collects and organizes all log and performance data from Azure resources, and you can access the activity logs for the last 90 days through steps in the console or CLI commands.
Using the Azure Monitor Log:
1. Open the Azure console, and navigate to the Activity log view. You can do this either by clicking into a specific resource or by searching for Azure Monitor to see all activity logs across your account.
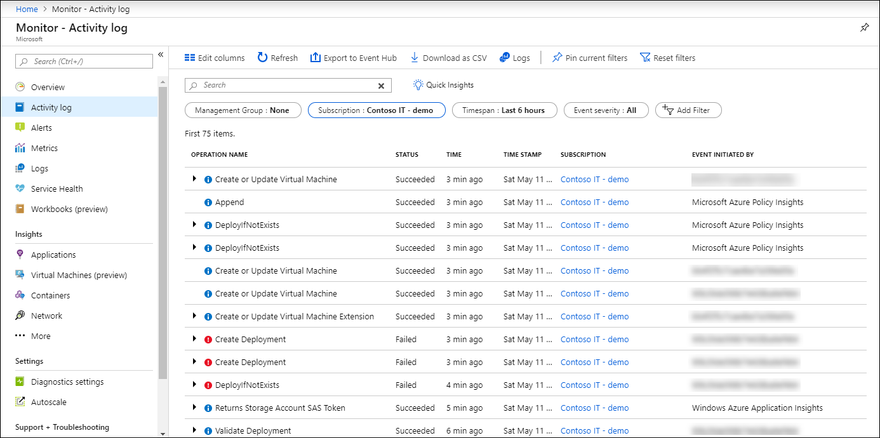
2. Next, you can add the Events initiated by filter to view only the activity logs related to a specific user.
3. You can also adjust the timespan filter to specify the full duration you care about. You can also select Edit columns if there is additional information you want to view.
4. To export the logs, click on Download as CSV.
This method is relatively simple, but it does require logging in to the console and manually working through the steps. Let’s look at running this same search from the Azure CLI.
Using the Azure CLI:
If you aren’t already set up with the Azure CLI, you’ll need to install it locally. From there, you can run the az monitor activity-log list command to list and query activity logs.
Here is the format to get the activity logs for a specific user:
az monitor activity-log list --caller [USER-NAME]
--offset [TIME-RANGE]
The offset parameter is formatted as XXdXXh, and defaults to 6h if not specified.
Here’s an example command to get the activity logs for John Smith:
az monitor activity-log list --caller john.smith@blinkops.com
--offset 14d
You can these additional parameters to modify the results:
- --start-time or --end-time: use the format of date (yyyy-mm-dd), time (hh:mm:ss.xxxxx), and timezone (+/-hh:mm).
- --resource-group, --resource-id, --namespace: use this to narrow to only activities affecting those specific resource areas.
- --max-events: use to change the limit of the results, the default is 50
You can see all of the options in the command documentation.
This approach is more easily repeatable than the console steps, but it requires you to remember the commands and be familiar with the Azure CLI.
With a no-code automation tool like Blink, you can run this task effortlessly.
Getting User Activity from Azure Faster with Blink
Retrieving user logs manually and adding them to a ticket could be a waste of valuable time, especially if your team is responding to a security incident.
With Blink, an automation can be triggered to pull and enrich Azure activity logs and other information for a compromised user right away.
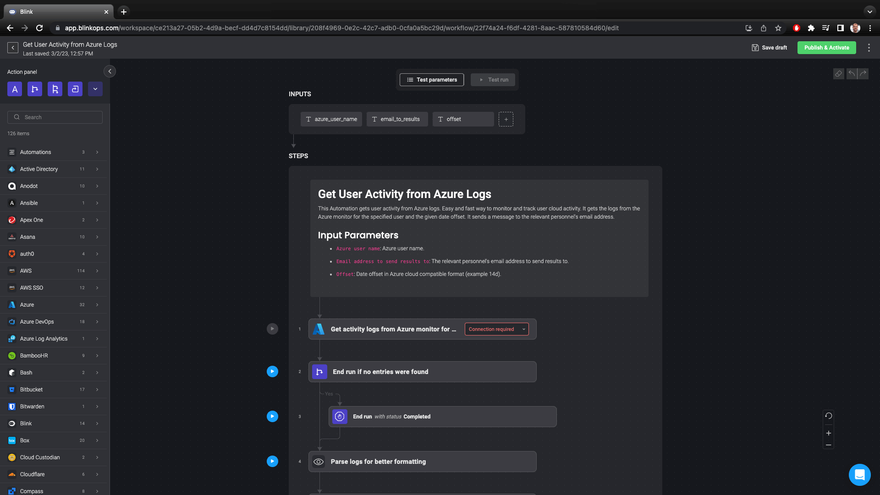
Blink Automation: Get User Activity from Azure Logs
The automation shown above is in the Blink library and is set up as a self-service app – where a team member can specify input parameters and get all the activity logs sent to an email address.
When it runs, it executes the following steps:
1. Fetches the logs from Azure monitor for a specified email address.
2. Formats the logs for better readability.
3. Reports the results to the specified email address.
If you’re handling a security incident, you can have this flow as part of an automation that is triggered by a malware or DLP alert for a given user. That way, you have all the logs and information you need to assess the risk for your organization.
You can import this automation from the library into your account and customize it based on your organization’s needs. For example, you can drag-and-drop new actions into the canvas or set up conditional subflows.
You can build your own automation from scratch or use one of our 5K pre-built automations today.
Start a free trial of Blink today or schedule time with us to see more.



Top comments (1)
@99 Nights in the Forest I appreciate the detailed steps for both the Azure console and CLI. It's great to have options based on my comfort level